Modern applications depend heavily on reliable data management. From banking systems and e-commerce platforms to enterprise resource planning tools and healthcare software, database systems must process transactions accurately and securely. Any inconsistency, data corruption, or system failure can lead to severe financial and operational consequences.
This is where ACID properties in DBMS become essential. ACID is a foundational concept in database management systems that ensures transaction reliability, consistency, and integrity.
In this comprehensive guide, we will explore:
- What ACID properties are
- Detailed explanations of Atomicity, Consistency, Isolation, and Durability
- Real-world examples
- Isolation levels and concurrency challenges
- ACID vs BASE comparison
- Advantages and disadvantages
- Performance tradeoffs
- Implementation best practices
By the end of this article, you will have a deep understanding of how ACID properties form the backbone of reliable database systems.
Table of Contents
What Are ACID Properties in DBMS?
ACID is an acronym representing four fundamental properties that guarantee safe and reliable database transactions:
| Letter | Property | Definition |
| A | Atomicity | A transaction is executed completely or not at all |
| C | Consistency | The database remains in a valid state before and after a transaction |
| I | Isolation | Concurrent transactions do not interfere with each other |
| D | Durability | Once committed, changes are permanently saved |
A transaction in DBMS is a sequence of one or more operations treated as a single logical unit of work. ACID ensures that even in the presence of failures, crashes, or concurrent access, database integrity remains intact.
1. Atomicity in DBMS
Atomicity ensures that a transaction is indivisible. It must either complete fully or have no effect at all.
If any part of a transaction fails, the entire transaction is rolled back.
Example: Bank Fund Transfer
Consider transferring ₹10,000 from Account A to Account B:
- Deduct ₹10,000 from Account A
- Add ₹10,000 to Account B
If the system crashes after deducting from Account A but before crediting Account B, the database would be inconsistent. Atomicity ensures that either both operations succeed or both fail.
How Atomicity Is Implemented
- Transaction logs
- Write-Ahead Logging (WAL)
- Rollback mechanisms
- Crash recovery systems
Risks Without Atomicity
- Partial updates
- Data corruption
- Financial discrepancies
- System instability
Atomicity is especially critical in financial and transactional systems.
2. Consistency in DBMS
Consistency ensures that a transaction brings the database from one valid state to another valid state, adhering to all predefined rules and constraints.
These constraints include:
- Primary key rules
- Foreign key relationships
- Unique constraints
- Check constraints
- Business logic rules
Example: Grade Validation
If a rule states that marks must be between 0 and 100, inserting 150 should fail. Consistency prevents such violations.
Database Constraints and Consistency
| Constraint Type | Purpose |
| Primary Key | Ensures uniqueness |
| Foreign Key | Maintains referential integrity |
| Unique | Prevents duplicate values |
| Check | Restricts value ranges |
| Not Null | Ensures mandatory data |
Consistency works closely with atomicity. If a transaction violates any constraint, it is rolled back entirely.
Why Consistency Matters
- Prevents invalid data states
- Maintains referential integrity
- Ensures regulatory compliance
- Protects business logic
In mission-critical systems, consistency is non-negotiable.
3. Isolation in DBMS
Isolation ensures that multiple transactions executing simultaneously do not interfere with each other.
Without isolation, concurrency issues may arise such as:
- Dirty reads
- Non-repeatable reads
- Phantom reads
- Lost updates
Common Isolation Levels
Database systems provide multiple isolation levels to balance performance and data integrity.
| Isolation Level | Dirty Reads | Non-Repeatable Reads | Phantom Reads | Performance |
| Read Uncommitted | Possible | Possible | Possible | Highest |
| Read Committed | Prevented | Possible | Possible | High |
| Repeatable Read | Prevented | Prevented | Possible | Moderate |
| Serializable | Prevented | Prevented | Prevented | Lowest |
Example: Ticket Booking System
Two users attempt to book the last available seat simultaneously.
Without proper isolation:
- Both users might see the seat as available.
- Both attempt to book.
- Data inconsistency occurs.
With isolation:
- One transaction locks the seat.
- The other transaction waits or fails.
- Only one booking succeeds.
Isolation often uses:
- Locking mechanisms
- Multiversion Concurrency Control (MVCC)
- Timestamp ordering
Higher isolation levels provide stronger consistency but reduce system throughput.
4. Durability in DBMS
Durability ensures that once a transaction is committed, its changes are permanently stored, even in the event of system crashes, power failures, or hardware malfunctions.
Example: Online Order Confirmation
After a customer completes payment and the transaction commits, the order must exist permanently in the database—even if the server crashes immediately afterward.
How Durability Is Achieved
- Write-Ahead Logging (WAL)
- Redo logs
- Disk persistence
- Database backups
- Replication mechanisms
Risks Without Durability
- Loss of confirmed transactions
- Financial disputes
- Customer dissatisfaction
- Compliance violations
Durability builds trust in digital systems.
ACID Properties Summary Table
| Property | Core Guarantee | Without It |
| Atomicity | All-or-nothing execution | Partial updates |
| Consistency | Valid state maintained | Rule violations |
| Isolation | No transaction interference | Concurrency anomalies |
| Durability | Permanent data storage | Data loss after crash |
Real-World Applications of ACID Properties
Banking Systems
Financial institutions depend heavily on ACID compliance to ensure:
- Accurate balance updates
- Fraud prevention
- Audit reliability
- Transaction traceability
E-Commerce Platforms
ACID ensures:
- Inventory accuracy
- Reliable order processing
- Payment integrity
- Cart management consistency
Healthcare Systems
Medical records must remain:
- Accurate
- Secure
- Consistent
- Durable
Errors in healthcare databases can be life-threatening.
Enterprise Resource Planning (ERP)
ERP systems rely on ACID to maintain consistency across:
- Payroll
- Inventory
- Procurement
- Accounting
ACID vs BASE – Modern Database Tradeoffs
In distributed systems and NoSQL databases, a different model called BASE is sometimes used.
ACID Model
- Strong consistency
- Strict transaction guarantees
- Ideal for financial systems
BASE Model
- Basically Available
- Soft state
- Eventual consistency
ACID vs BASE Comparison
| Feature | ACID | BASE |
| Consistency | Strong | Eventual |
| Performance | Moderate | High |
| Scalability | Limited | High |
| Data Safety | High | Moderate |
| Best For | Banking, ERP | Social media, analytics |
Many modern NoSQL systems now support partial or scoped ACID compliance to combine performance with reliability.
Performance Tradeoffs of ACID
ACID guarantees come at a cost.
Overhead Factors
- Locking mechanisms
- Transaction logging
- Disk I/O operations
- Synchronization processes
Performance vs Consistency Visualization (Conceptual)
As consistency increases:
- Performance may decrease
- Latency increases
- Throughput reduces
Database architects must choose isolation levels and configurations carefully.
Advantages of ACID Properties
- Ensures complete data integrity
- Prevents corruption during failures
- Supports concurrent user operations
- Provides reliable crash recovery
- Maintains compliance with regulations
- Strengthens customer trust
Disadvantages of ACID Properties
- Performance overhead
- Reduced scalability in distributed systems
- Increased hardware requirements
- Potential locking contention
- Higher complexity in configuration
Despite these tradeoffs, ACID remains the gold standard for transactional systems.
Best Practices for Implementing ACID in Applications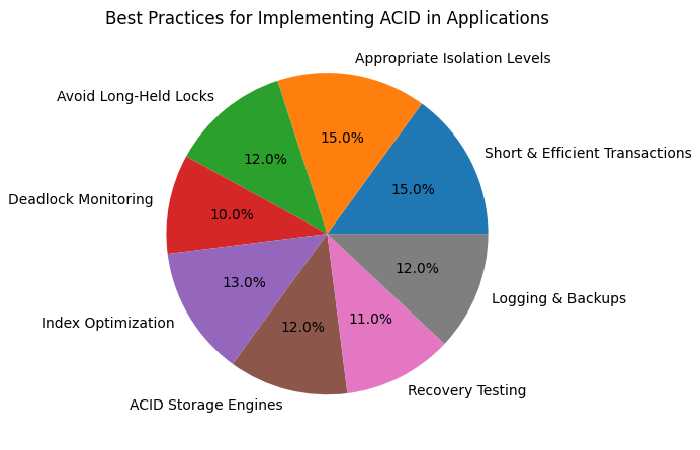
Implementing ACID properties effectively is not just about using a relational database. It requires thoughtful system design, performance planning, monitoring, and operational discipline. Below is a detailed breakdown of the most important best practices that help ensure strong ACID compliance without sacrificing scalability and performance.
Keep Transactions Short and Efficient
Short transactions are critical for maintaining both performance and reliability in ACID-compliant systems.
Why It Matters
- Long-running transactions hold locks for extended periods.
- They increase contention in high-concurrency environments.
- They consume memory and log resources.
- They raise the risk of rollbacks due to failures.
Best Practices
- Perform validation logic before starting the transaction.
- Avoid user interaction during an active transaction.
- Do not include network calls inside a transaction block.
- Commit immediately after completing required operations.
Example: Good vs Poor Design
Poor Design
- Start transaction
- Call external API
- Wait for user confirmation
- Update database
- Commit
Good Design
- Validate inputs
- Call external services
- Start transaction
- Perform database operations
- Commit immediately
Keeping transactions concise reduces deadlocks and improves throughput under load.
Choose Appropriate Isolation Levels
Isolation levels directly impact both data integrity and system performance. Choosing the correct level depends on the application’s consistency requirements.
Common Isolation Levels
| Isolation Level | Use Case | Performance Impact |
| Read Uncommitted | Reporting systems | Minimal overhead |
| Read Committed | Most web apps | Balanced |
| Repeatable Read | Financial apps | Moderate overhead |
| Serializable | Critical financial systems | Highest overhead |
Selection Strategy
- Use Read Committed as the default for most applications.
- Upgrade to Repeatable Read for financial consistency.
- Use Serializable only when absolute correctness outweighs performance concerns.
Avoid setting the highest isolation level system-wide unless required. Overuse of Serializable can significantly reduce concurrency.
Avoid Long-Held Locks
Locks are essential for isolation but can become a performance bottleneck when held too long.
Problems Caused by Long Locks
- Blocking other transactions
- Increased wait times
- Reduced throughput
- Deadlock scenarios
Best Practices
- Keep transaction scope minimal.
- Access rows in consistent order across transactions.
- Use row-level locking instead of table-level locking when possible.
- Avoid scanning large datasets within transactions.
Efficient lock management is central to scalable ACID compliance.
Why ACID Properties Are Still Critical in 2026
Even as cloud-native and distributed architectures evolve, ACID remains fundamental for:
- FinTech platforms
- Payment gateways
- SaaS billing systems
- Government databases
- Enterprise software
While scalability models evolve, the need for reliable transaction management remains unchanged.
ACID properties ensure that digital systems behave predictably under stress, concurrent access, and unexpected failures.
Final Conclusion
ACID properties in DBMS — Atomicity, Consistency, Isolation, and Durability — define the reliability standard for database transactions.
They ensure that:
- Transactions execute completely or not at all
- Databases remain valid at all times
- Concurrent operations do not conflict
- Committed changes are permanently stored
Although implementing ACID introduces performance and scalability considerations, its guarantees are essential for any application handling critical data.
For developers, database architects, and technical professionals, mastering ACID properties is not optional — it is foundational knowledge for building robust and trustworthy systems.

